I don’t know if any of you have ever encountered this situation: when you wake up, the APP on your phone quietly updates automatically. Not only did the icons change, but the most uncomfortable thing was that the originally smooth operation logic and page layout were completely messed up overnight.
But if you are using an Android phone at this time, congratulations, you can find a third-party APK mirror site, or ask a friend to send you the installation package of the previous version, and install it back manually. Basically, you can freely "downgrade" the APP.
It is precisely because of this that the Android system has always given people the impression that "although it is a little troublesome, users still have the final say on many things."
And this is exactly what Google has been emphasizing for so many years: open source spirit and freedom.
But starting this year, the good days for Android users may be coming to an end.
Here's the thing -
On March 19, Google, which has always advertised open source and freedom, announced a decision that violated its ancestral precepts and officially announced the launch of the "advanced installation flow" for Android sideloaded applications.

The so-called "sideloading" means that the user installs the APP from a third-party source without going through the official app store, which is the situation we mentioned at the beginning. And this kind of design, packaged as "protection", falls on the user, and the feeling is actually closer to "restriction".
In order to make it easier for readers to understand, Tony will take the domestic app store as an example for the time being.
Before Google's new rules were implemented, most Android phones that wanted to install an application from an unofficial store could install it normally by clicking "Allow Unknown Sources" - the domestic version of Android phones might require you to enter an additional password, but that's about it at most.
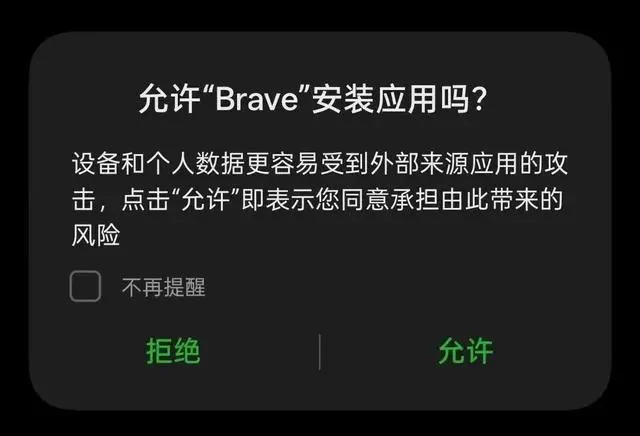
It is equivalent to the old rules being just a disclaimer. The system only provides risk warnings. It is up to you to decide whether to install it or not. But after the implementation of this new advanced protection mechanism, the logic changed.
The system no longer simply determines "whether this application comes from the official app store", but also further determines whether the developer behind the application has completed registration and verification with Google.

And this "verification" is quite troublesome. It's not just a matter of just filling in the information. Developers publishing apps outside of Google Play must provide proof of identity and pay a $25 registration fee.
Assuming that the developer has not completed the verification, the process for ordinary users to install this third-party APK will become very cumbersome. The steps include but are not limited to -
Click the system version number 7 times in succession to open developer options
Allow installation of unverified packages
Enter your device unlock PIN or password
Restart device
Wait 24 hours
Select "Temporarily Allow" (7 days) or "Permanently Allow"
Check the risk confirmation box and install anyway
I don’t know how the missionaries felt when they saw this. Anyway, my first reaction was: I installed an app on my mobile phone, but why did it look like I was trying to break through a level...
So what Google did this time was not, as rumored outside said, "Android will no longer allow the installation of third-party APKs in the future." Instead, it hid the entrance that allows installation in a very hidden way, and the steps were extremely long.
To put it bluntly, this trick is to put the brakes on sideloading fraud at the physical level. Although this will indeed disgust you, Google hopes to reduce the harm of rogue software and scam software in this way——
On the one hand, a forced restart can directly cut off the call between the scammer and the victim; on the other hand, the 24-hour restriction period also lengthens the installation process as much as possible, giving the victim time to respond to determine whether he or she has been deceived.
Google also has its own difficulties in launching this mechanism.
In recent years, software security issues have become more and more prominent. The openness that Android has always been proud of has increasingly become Google's biggest headache.
Official data illustrates the problem: users are 50 times more likely to download malware outside of Google Play than in Google Play.Because of this, the most direct goal of this new regulation is to combat fake applications, fraudulent software, and malicious programs.
And judging from the pace of implementation, the enforcement of this new set of regulations will also start in markets such as Brazil, Singapore, Indonesia and Thailand. The explanation given by Google is that the problems of impersonation scams and inducement scams faced in these areas will be more prominent...
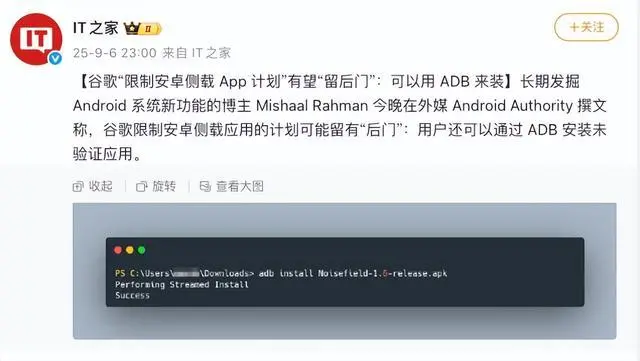
At the same time, Google has not cut off all unofficial installation paths across the board. As for development and debugging, internal distribution within the company, and small-scale sharing by amateurs, the official still leaves a hole -
For example, the ADB workflow, that is, installing applications through the command line, has been clearly retained; enterprise devices and internal application stores within organizations are not affected by the new regulations; for individual developers, Google has also prepared a free "restricted distribution account" that does not require submission of government identity documents, but can only be shared with a maximum of 20 authorized devices.
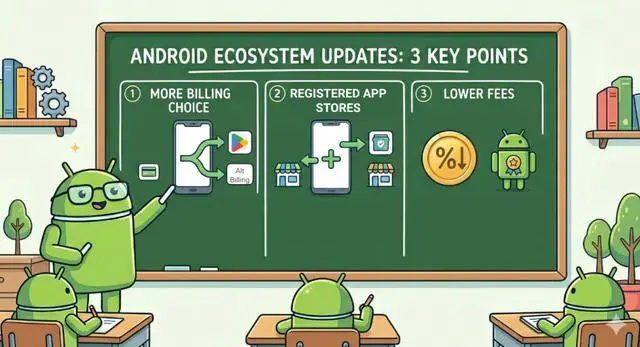
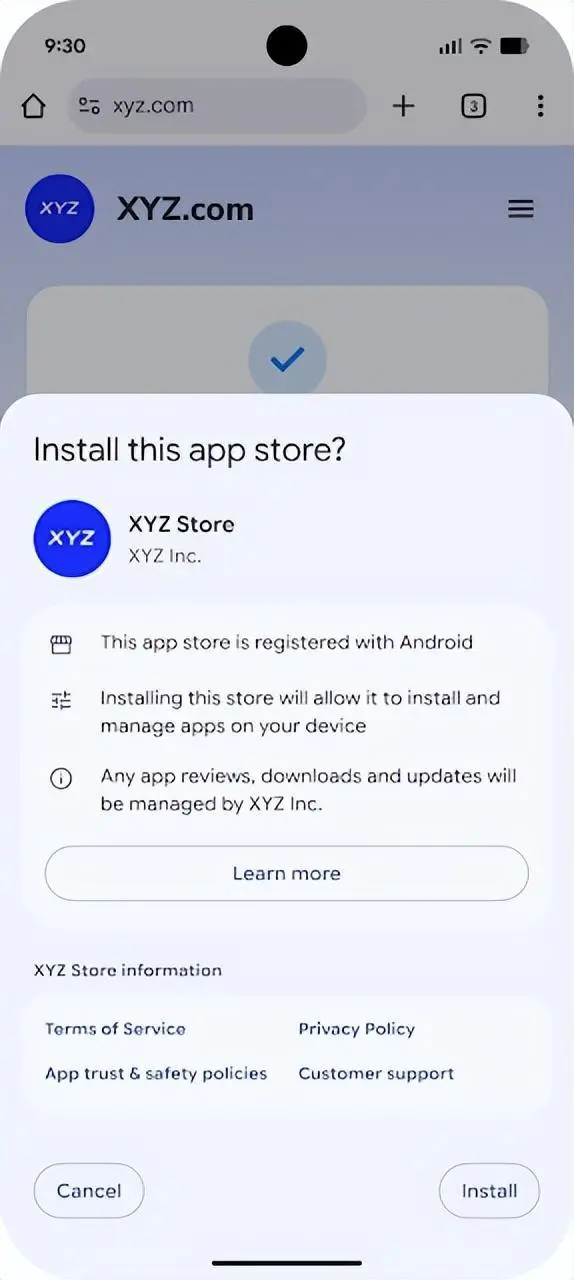
In addition, Google also reserves a smoother installation channel for qualified third-party app stores.
This also means that what Google really wants to tighten this time is not all sideloading, butOpen sideloading for ordinary users,There is a high probability that you are reading this article...
In other words, it is not to directly sentence Android sideloading to death, but to firmly hold the matter of "who is publishing the App, in what capacity, and through what channels" in its own hands.
But the problem lies precisely here. At least judging from the current public opinion reaction, many people do not believe that Google will stay at the "identity verification" step.

After all, once the platform completely figures out "who you are," the liability risks that independent developers will face will only get higher and higher in the future; and anonymous publishing, independent distribution, and small-scale developers will also be squeezed out of their living space.
However, disputes are disputes. Who this set of rules will ultimately control depends on which devices it actually falls on.
The answer probably has to go back to Google's announcement itself. The most noteworthy thing here is not actually the words "restrict sideloading", but the premise specially added by Google: for certified Android devices, which translated into vernacular is——
This new set of regulations governs equipment that has been "certified by Google itself and obtained GMS authorization." Products such as Pixel, Samsung overseas version, and Xiaomi international version, which come with Google Play and Google services from the factory, basically fall into this category. It’s hard to say yet whether domestic Android users will be affected.
Fortunately, according to current information, the "sideloading threshold" added by Google this time is most likely not written directly into the Android open source bottom layer (AOSP), but added to the GMS / Google Play Services layer.

This point is actually very critical.
Because once this set of things is shoehorned into AOSP, the nature of the matter completely changes. That's not just "enhancing security and preventing fraud", but directly touching the open logic at the bottom of Android that "anyone can use it and anyone can change it". If it really gets to that point, Google will not only face complaints from users, but also the developer circle will spray it to death.
But if this mechanism is just put into GMS, Google's statement is much more respectable: I didn't touch the entire Android, I just added an extra layer of protection to the devices that use my authentication service.
But the problem is that no matter which layer it ends up on, when installation permissions, distribution paths, and even developer qualifications begin to be redefined by the platform, the original open and independent temperament of Android is actually fading away little by little...